You are born private.
Your thoughts are private.
You are your thoughts.
Data is the reflection of your thoughts.
Systems ought to make your data private
Right when your data is born
Until deleted by you
Everywhere.
Protect your data.
Protect your thoughts.
Protect you.
Everywhere.
That’s NUTS.
Internet of Data
IoD™: The Internet of Data™
By Yoon Auh, Founder of NUTS Technologies, August 27th, 2022.
The Internet of Data™ (IoD™) enables direct access to data across any network. Accessing data directly is possible when data has at least two characteristics: identification and privacy.
Identification of Data
Identification of objects is conventionally implemented within narrow scopes such as VIN, SSN, cell number, MEID, MAC, IPv4, IPv6, etc. For IoD, any data is eligible for permanent identification using a Practically Unique ID (PUID) by any capable device.
Identification of data is as narrow or broad as required and easily implemented with an identifier: the larger the identifier, the bigger the possible universe of data. A large enough identifier can identify the data across space and time. The size of the data identifier can start small and grow as needed; as implemented, this identifier is defined as the NutID. NutIDs are unstructured identifiers to maximize anonymity; this has the implied consequence of making brute force guesses very expensive for an identifier to a piece of data.
Privacy of Data
Privacy of data is conventionally controlled through access gateways and obfuscations (ciphering), each of which present numerous technical challenges when done at scale. To secure data for IoD, it is convenient to have a compact, fine grained, access control system that is cryptologically implemented as data; we define data secured by a compact, independent, portable access control system as Zero Trust Data (ZTD). Other equivalent terms for ZTD are “Secure Container” and “Security at the Data Layer”.
A Secure Container implemented as an encapsulation can be used to envelope the payload to accommodate a wide variety of object and file formats. Within the secure container, any metadata is also protected (immutable).
We define a simple nut container as a secure container with an immutable NutID as metadata and the data to be protected as the payload where the access controls are expressed as sets of cryptographic keys configured into progressively revealing data structures.
Thus, data in a nut can be accessed directly by any key holder(s) on the Internet of Data.
Independent Data
Data in a nut is independent data. An IoD ecosystem can provide transport and locate services for independent data across any network. The nut can be addressed directly by its NutID, further, the nut can address other nuts by their respective NutIDs; therefore, a NutID is a permanent reference to a nut in contrast to impermanent URL paths. In essence, the secure container protects and identifies its payload. A nut with a payload of NutIDs is an example of data directly addressing other data.
It is nontrivial to store and forward URLs by other web servers, whereas a nut can be handled by any relay mechanism due to its intrinsic security and portability. URIs and URLs are ever changing and may not be the same the next time you visit them. Documents not visible to web searches are very difficult to track down. Document authentication is even more difficult. In contrast, a NutID of a document will never change and references the actual document which will self-authenticate upon presentation of a valid key.
Independent data in a nut protects its payload and only the key holder(s) can easily access it; therefore, a nut can be safely stored anywhere on the IoD. Expressed as a generic file format such as JSON-base64, a nut is independent of most Operating Systems, File Systems and Cloud Systems. Getting a copy of a random nut is not enough to access its contents, one must present a valid credential in the form of cryptographic key. Since the access controls for the nut are embedded within its container material as cryptographic data elements, the payload is consistently protected in any environment independent of reference monitors.
Key Management
A secure system requires the safekeeping of secrets such as cryptographic keys in a systematic way on behalf of the user; a nontrivial problem. In the evolving world of data security, the ownership of cryptographic keys is an important factor in establishing the ownership of ciphered data. Both concerns can be addressed effectively and simply within a IoD implementation using nut containers.
IoD as implemented by the NUTS ecosystem provides each user installation with a key management system (KMS) built on nut containers. Since a nut identifies and protects a payload of any storable digital data, a cryptographic key or digital credential stored as payload in a nut is private and an identified in a universal way.
A nut container can be configured with an arbitrary number of keyholes each of which is identified by a NutID (or within this context, a KeyID). This presents the raw building blocks to construct a secure, robust and modular KMS using nuts as key carriers: a simple, elegant, logical and massively scalable design.
Conclusion
Our research shows that when properly engineered, IoD can provide an individual user with features often associated with the most sophisticated IT organizations such as hybrid cloud data management, data resiliency, ransomware mitigation, insider threat mitigation, automatic backup, hot backup, secure data sharing, automated synchronization, cipher agnostic cryptography, on device key management, and key ownership. All of these features in one ecosystem in an integrated fashion expressed as protected, identifiable data storage units.
Conventional approaches may provide most of the features listed above but may require many solutions to be configured simultaneously by knowledgeable people with integration as an secondary concern. Insider threat mitigation is only attempted by organizations with deep pockets and the need whereas the NUTS ecosystem delivers Insider Threat mitigation within every nut container in an independent way; the epitome of Zero Trust Data.
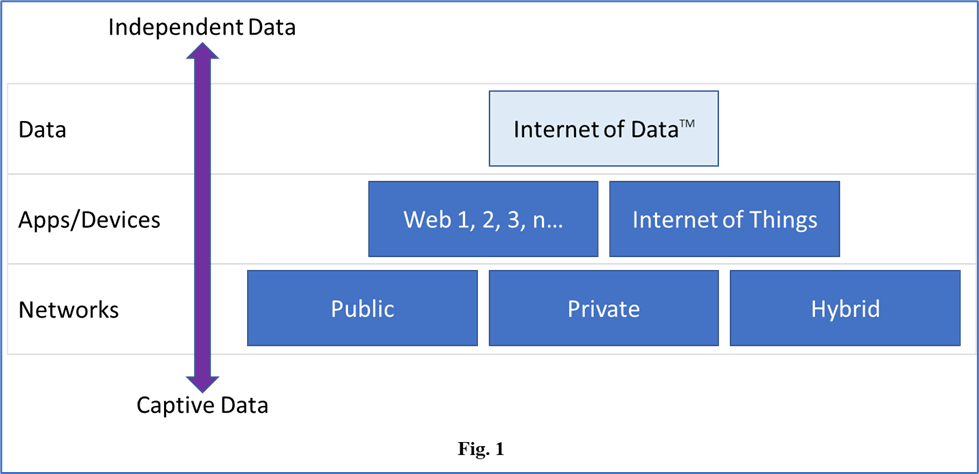
The Internet of Data establishes a new abstraction layer for the way we can interact with data and the way data can interact with other data (Fig. 1). IoD puts forth an environment where Operating Systems, File Systems and Networks are commoditized and your Data is prioritized.
In all honesty, does any user authenticate into a system for the pure pleasure of logging into a system? No, because, in the end, it’s all about the Data.
You’re Invited to our Annual NUTS Technologies DC CyberWeek Event!
We hope you can join us this coming October 22nd for our annual DC CyberWeek showcase.
Come on down, grab a cup of coffee, and learn a bit more about the groundbreaking developments happening at NUTS Technologies.
This year’s event will feature:
• Structured Cryptographic Programming…
• Structured Data Folding with Transmutations…
• Quantum Resistant Cryptographic Framework…
• and DNA Inspired Data Centric Design
We are also excited to announce this year’s presentation will be accompanied by a demonstration of the NUTS prototype! We look forward to walking you though how NUTS implements object level controls of security at the data layer and beyond…
Event Details:
Date: October 22nd, 2019 | 9:00 – 11:00 am
Venue: DLA Piper Building, 500 8th street, NW, Washington, DC 20004
Price: This event is FREE to attend but seats are limited, so register today to reserve your spot!
Event Link: “Implementing Object Level Controls for Security at the Data Layer”
https://2019dccyberweek.sched.com/event/Kr9g/implementing-object-level-controls-for-security-at-the-data-layer?iframe=no&w=100%25&sidebar=yes&bg=no
If you have an interest in data Security, Privacy, and ‘Need to Know’, you won’t want to miss this event. We look forward to seeing you there!
All the best,
NUTS Technologies Team
info@nutstechnologies.com
www.nutstechnologies.com
Upcoming Event – NUTS Demonstration at DC CyberWeek 2019
Don’t miss your chance to witness the first public unveiling of the NUTS beta demonstration at DC CyberWeek 2019 in Washington D.C. Tuesday Oct 22nd @ 9AM,
“Implementing Object Level Controls for Security at the Data Level”
Paradigm Shift: Thomas Kuhn defined the term to describe the periodic upheavals in the progress of scientific knowledge. Can you recognize a paradigm shift if you saw one?
The title of the presentation is directly from an active DoD RIF. We will show you what that future looks like in a working demo, and the future lands on a Tues morning in October. From data structures to custom protocols, all with security integrated organically. What does that last statement mean? What does such a thing look like? How does it function? How can it be utilized?
We are presenting in the heart of D.C. at the DLA Piper building. Refreshments and snacks will be served. Come hungry in mind and body. You won’t be disappointed. Bring your colleagues.
You can register for the event by clicking on the link below
Regards,
NUTS Technologies Team

We are back at DC CyberWeek 2018!!
![]() NUTS Technologies is happy to announce that we were invited back to host at DC CyberWeek 2018.
NUTS Technologies is happy to announce that we were invited back to host at DC CyberWeek 2018.
Register now for ‘The God Complex: Temptations of the Forbidden Fruit in the Digital Garden’ on Tuesday Oct 16 at the DLA Piper Building, Washington DC.
Event page http://sched.co/G8Fq
General conference information can be found here
We will be hosting a DC CyberWeek event!
Join us in Washington D.C. in 2 weeks.
Register now for Socratic Dialogue: The God Key Problem on Oct 17 at CyberScoop’s DC CyberWeek: http://bit.ly/2tNjT42
Event page http://sched.co/CUVI
This will be an old school discussion on The God Key Problem and its solutions.
The God Key Problem: Digitizing the Dynamic Nature of Trust
By Yoon Auh, Founder of NUTS Technologies, Inc., the world leader in Data Centric Designs of secure data systems.
Snowden. We only have to mention this single name to conjure up a plethora of views on the matter that plastered the headlines in 2013. Regardless of your personal views on the matter between the US Government and its ex-consultant, there are two main issues that this incident highlights and should be addressed objectively: 1) the dynamic nature of trust and 2) the God Key problem.
Trust is serious business. We depend on trust in each other, in social systems, in courts, in childcare, in policing, and many other societal foundations in order to live a relatively secure and care free lives. Our trust in the sanctity of contracts, law and its enforcement mechanisms and the continuity of trust enables the average person to earn a living and plan their futures decades in advance. But trust changes over time. It is dynamic. This is why there are laws and the enforcement of those laws in order to keep everyone in a position of trust in check.
The dynamic nature of trust is something everyone learns and understands over time when growing up. It changes a lot especially when it comes to interpersonal relationships. If this were not the case, why would our national divorce rate be close to 50%? This happens more frequently in our professional lives and is generally considered a healthy thing. The senior engineer you entrusted your next big project to is jumping ship to a competitor to get more responsibility and better pay. Your top portfolio manager is leaving after establishing a track record at your firm to become a partner at a fast growing hedge fund. Even in the brutal world of drug trafficking, the betrayal of trust is dealt with terminal violence.
The nature of trust is mutual, unilateral and exquisitely temperamental. Both parties rely on the passage of future events to determine their level of trust in one another; therefore trust is mutual between the two parties. Trust is built over time by many trustful deeds and events between the two entities. The first instance of an untrustworthy event may nullify the entire history of trust in the relationship. The intended trustful relationship is unilateral because each party may independently violate the trust in the relationship. Whether the violating party decides to alert the other party to this change in the relationship results in the complicated saga of betrayals.
The trust in a relationship is further complicated by adding in the self-interest priorities of each participant. It’s a quagmire of chess-like strategies with imperfect information.
The God Key problem is an age old computer science issue and is a principal culprit of most cybersecurity scandals and hacks. Most computers designed and manufactured today have an administrative mode of operation which gives the user unfettered access to everything within the computer’s domain or physical hardware. There are some exceptions to this but this is the predominant model. Most companies that rely on computer processing for their business operations will have a group of administrators who have the God Key to all the business systems in the company. This is a necessary evil since computer systems do not administer themselves and they are in constant need of maintenance in both software and hardware. The God Key is not just one all access key, but it’s the combination of access credentials that are given to administrators to allow them unfettered access to all the systems within their domain.
In most corporate settings I’ve been in, it’s been a naturally occurring event to see smart young technically adept individuals being given ready access to the God Key of corporate systems and networks. Much of advanced technology is tamed by young people who are fresh out of school with the latest knowledge and techniques. Sometimes the best ones are self taught and nerdy renegades answering to the siren call of large paychecks for performing tasks they would do for free on their own time just for the hell of it. We sometimes call these people hackers both white hat and black hat.
The most frustrating thing about this situation is the quandary that managers are facing when pressed for time and talent in a crisis: who do you give the God Keys to so the job can get done in a hurry? You give it to the most skilled operator. In the world of IT, the most skilled does not correlate to the most experienced, the most knowledgeable, the most seasoned, nor the most trustworthy. The operator who is given the God Key may have been deemed trustworthy at one point but that trust may have changed over time. How is an institution supposed to measure that? How do they keep track of that? What if the operator hides the fact to his employer that he cannot be trusted anymore?
Snowden. This is exactly the scenario that played out between the NSA and Snowden. The dynamic nature of trust sucks in a digital world, even to the NSA who is in the business of trust. The point is that this problem exists in every institutional computer system. The NSA has plenty of company. Everyone deals with these problems in one way or another but most conventional ways are inadequate and does not address the issues related to the dynamic nature of trust.
To solve this thorny problem, you need to be able to separate the ability to administer the system from the ability to read everything within its domain. Most complex systems are designed to be centrally controlled. They may have distributed access, distributed storage or distributed processing, but administration is usually tightly controlled in a central manner. What company doesn’t like control? In fact, most institutions in the free world are hierarchically structured like little dictatorships. But these structures work and people adapt to them naturally so it is the predominant organizing mode of mass productivity.
All the sensitive data of the company needs to be secured to block out the curious gaze of the system administrators. We have many systems to do such containments but most of them require central management and some version of authorization token based access control: you see the circular logic problem here, central management requires an administrator with the God Key to that particular system which raises the same issues.
The solution lies in data containers that can act as its own reference monitors working with a truly independent and distributed key management system.
This problem took me over 5 years to solve. Along the way, the solution set that was crafted solved many other nagging issues. The approach that I came up with is called Data Centric Design. It is unrelated to any definition of Data Centric Design on the web today. This is a new technology. It is a radical technology. It is an adaptive technology.
It forges Applied Cryptography in new ways to construct a framework where Data can grow up and do some things for itself. That’s right. Data is personified in that last sentence. It’s about time that Data got smarter and learn a few tricks of its own rather than depending on applications to wipe its butt every time because we are learning that the butt wipers are not all that trustworthy nor competent in this computerized world of ours.
Welcome to the world of eNcrypted Userdata Transit & Storage or just NUTS!
Welcome
Welcome to the NUTS Technologies blog. We are currently under construction and will be uploading content soon